Every year, security teams proudly complete their VAPT cycle. Reports are shared. Critical findings are fixed. Compliance boxes are checked. Leadership feels reassured.
And yet, breaches still happen.
Not because VAPT is ineffective. But because the digital environment it tests changes far faster than most organizations realize.
If your company performs Vulnerability Assessment and Penetration Testing regularly, that is a strong foundation. But in today's cloud-driven, API-connected, rapidly deployed world, VAPT alone is no longer enough. This is where External Attack Surface Management (EASM) becomes critical.
Let's unpack why.
VAPT Is a Snapshot. Your Attack Surface Is a Living System.
A VAPT engagement tests a defined scope at a specific moment in time. It is thorough within that boundary. Skilled testers simulate real-world attackers and attempt to exploit weaknesses.
But the keyword here is defined.
The testing team can only assess what they are told exists.
Now think about how modern infrastructure works. New cloud instances spin up in minutes. Development teams deploy staging environments. Marketing launches microsites. Vendors integrate APIs. Certificates expire. DNS records change.
Your external footprint is dynamic.
By the time your VAPT report is finalized, your attack surface has already changed.
External Attack Surface Management provides continuous visibility into what is exposed to the internet. It does not wait for an annual schedule. It watches your perimeter as it evolves.
You Cannot Protect What You Do Not Know Exists
One of the biggest risks organizations face today is unknown exposure.
Security teams typically maintain an asset inventory. But business units move fast. Developers experiment. Cloud platforms make it easy to deploy infrastructure without centralized approval.
This creates shadow IT.
External Attack Surface Management continuously discovers internet-facing assets associated with your organization. Domains, subdomains, IP ranges, exposed services, cloud storage, forgotten test environments. It shows you what an attacker can see.
And attackers always start with reconnaissance.
They do not care about your internal asset register. They scan the internet, map your digital footprint, and look for the weakest entry point. If there is an exposed development server or an outdated API endpoint, that becomes the path of least resistance.
VAPT may never test it if it was not included in scope.
External Attack Surface Management ensures that blind spot does not exist.
How EASM Transforms Every VAPT Phase
The relationship between VAPT and EASM is not either-or. EASM enhances every stage of your security testing—from discovery through remediation. Here is how they work together:
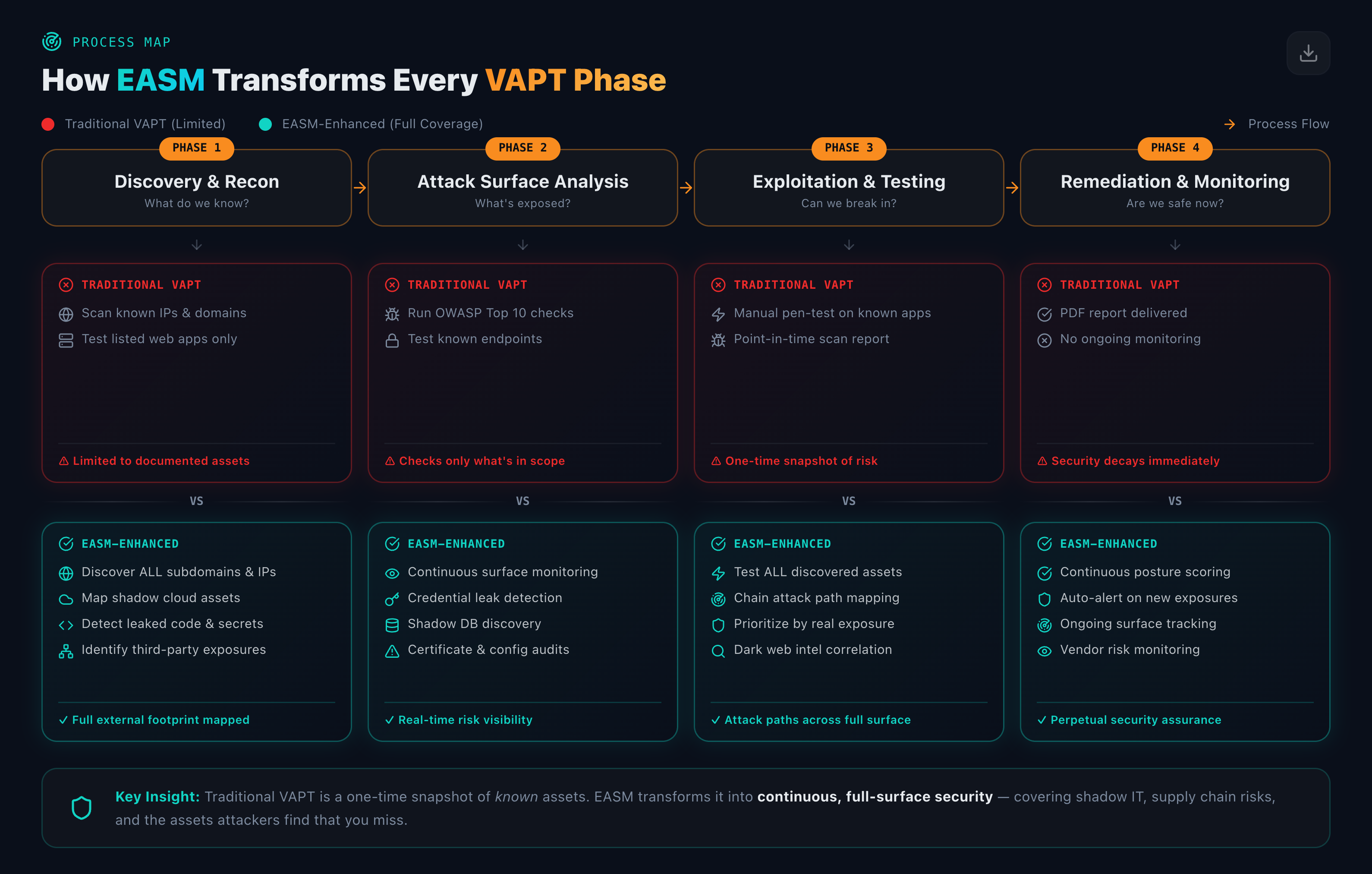
Discovery & Recon: Traditional VAPT scans known IPs and domains. EASM discovers all subdomains, maps shadow cloud assets, detects leaked code and secrets, and identifies third-party exposures. Result: your full external footprint mapped.
Attack Surface Analysis: VAPT runs OWASP Top 10 checks on what is in scope. EASM provides continuous surface monitoring, credential leak detection, shadow database discovery, and certificate audits. Result: real-time risk visibility.
Exploitation & Testing: VAPT delivers a point-in-time report. EASM enables testing of all discovered assets, attack path mapping across the full surface, and prioritization by real exposure. Result: attack paths across your entire perimeter.
Remediation & Monitoring: VAPT delivers a PDF and stops. EASM provides continuous posture scoring, auto-alerts on new exposures, ongoing surface tracking, and vendor risk monitoring. Result: perpetual security assurance.
Traditional VAPT is a one-time snapshot of known assets. EASM transforms it into continuous, full-surface security—covering shadow IT, supply chain risks, and the assets attackers find that you miss.
Compliance Is Not the Same as Security
Many organizations conduct VAPT because standards such as PCI DSS, ISO 27001, and SOC 2 require it. Compliance is important. It enforces discipline.
But compliance-driven testing is periodic.
Attackers are continuous.
External Attack Surface Management shifts the mindset from passing audits to maintaining visibility. It focuses on exposure reduction in real time. It answers questions like:
- What new services became publicly accessible this week?
- Did any cloud storage bucket become open to the internet?
- Are there newly exposed ports that were previously closed?
- Has a certificate expired, weakening encrypted communication?
These are not theoretical risks. They happen every day in growing organizations.
Modern Breaches Often Start Outside the Core Application
When leadership thinks about security testing, they often picture someone attacking the main web application.
In reality, breaches frequently begin with overlooked assets. A misconfigured server. An exposed administrative interface. An unprotected API. A forgotten staging environment.
External Attack Surface Management maps these peripheral exposures.
VAPT then goes deeper.
Think of it this way: External Attack Surface Management tells you where your doors and windows are. VAPT tests whether they can be broken.
Without knowing all your doors and windows, even the best penetration test cannot guarantee full coverage.
The Speed of Cloud Has Changed the Game
Cloud adoption has fundamentally expanded the attack surface. Infrastructure as code, containerization, multi-cloud environments, remote work infrastructure, third-party integrations. Each adds new external touchpoints.
Security teams are expected to keep pace, but manual inventory processes cannot scale with cloud velocity.
External Attack Surface Management automates discovery across your internet-facing footprint. It identifies exposed services, misconfigurations, and risky technologies continuously.
This allows security teams to remediate early—often before an attacker notices.
VAPT remains essential for validating real exploitability. But External Attack Surface Management ensures nothing slips through the cracks between engagements.
Continuous Visibility Reduces Risk Between VAPT Cycles
Consider a typical annual VAPT model.
Testing happens in January. Critical findings are fixed by March. The rest of the year is quiet from a testing perspective.
Now imagine a new microservice is deployed in June with a configuration error that exposes an admin panel publicly. No one notices.
An attacker scanning the internet in July finds it.
The breach happens in August.
The next VAPT is scheduled for the following January.
This gap is where External Attack Surface Management adds immense value. It identifies new exposures as they appear, not months later.
Security becomes proactive instead of reactive.
VAPT and EASM Are Complementary, Not Competing
It is not a question of choosing one over the other.
VAPT provides depth. It simulates real attacks, validates vulnerabilities, and exposes business logic flaws.
EASM provides breadth. It ensures complete visibility of your internet-facing environment and monitors it continuously.
Together, they create a mature security posture.
- External Attack Surface Management defines and monitors the battlefield.
- VAPT stress-tests your defenses within that battlefield.
Organizations that rely only on periodic testing risk missing the unknown unknowns. Those that combine continuous external visibility with expert penetration testing significantly reduce their exposure window.
The Bottom Line
If your company is already doing VAPT, that is a strong step forward.
But ask yourself a simple question:
Are you absolutely certain you know every single asset exposed to the internet right now?
If the answer is not a confident yes, then External Attack Surface Management is not a luxury. It is a necessity.
In a world where digital footprints expand daily and attackers operate continuously, visibility is the first layer of defense.
And you cannot defend what you cannot see.